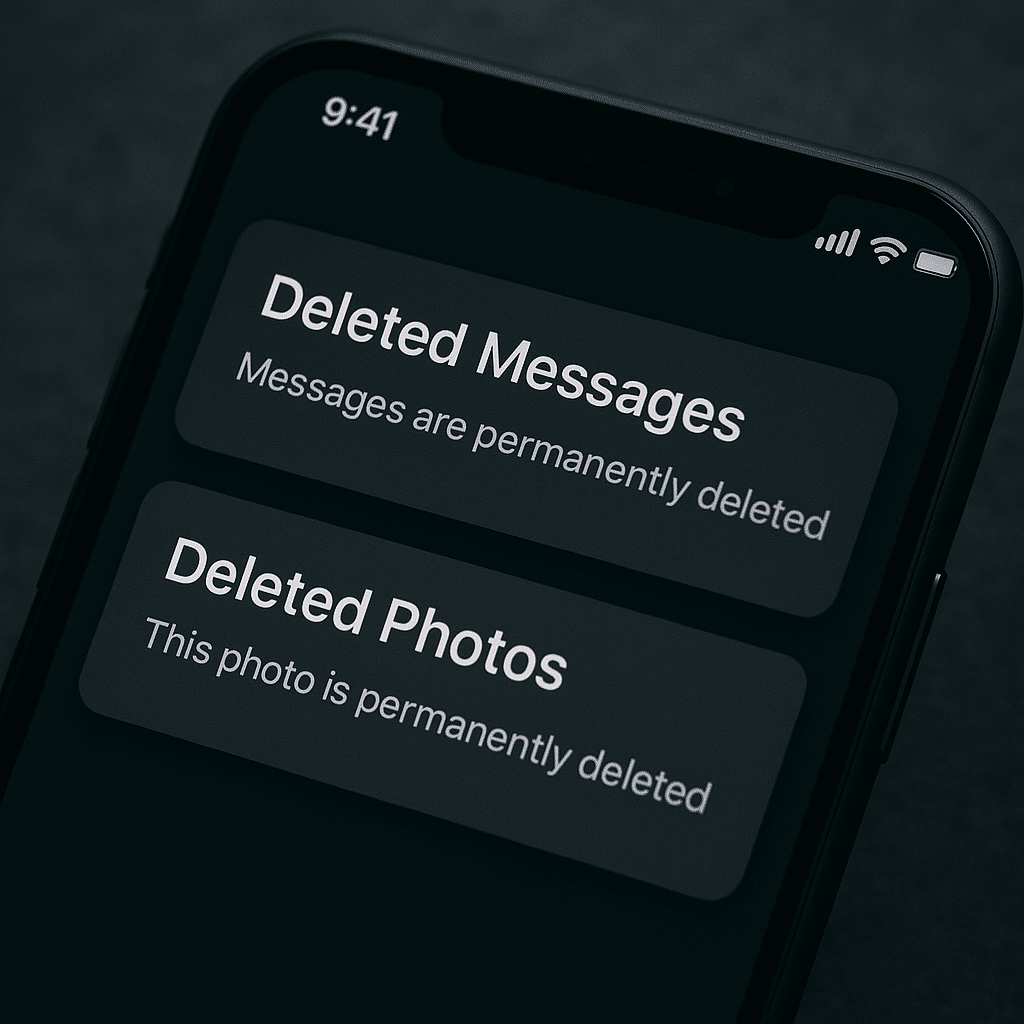
Apple has quietly patched a serious iOS vulnerability that could allow deleted messages to be recovered and the implications go far beyond a typical software bug.
The issue, which affected both iPhones and iPads, stemmed from how iOS handled notifications. Even after users deleted messages including those from privacy-focused apps like Signal, remnants of those conversations could still persist in the system’s notification database, effectively leaving behind recoverable traces.
That’s not how most users think deletion works.
In theory, deleting a message should remove it entirely. But in this case, the operating system retained copies of message content through cached notifications, sometimes for extended periods reportedly up to weeks even after the original app data was gone.
And that created a loophole.
Reports suggest that forensic tools and in some cases law enforcement were able to exploit this behaviour to recover messages that users believed had already been permanently deleted.
Apple has now addressed the flaw with updates including iOS 26.4.2 and corresponding iPadOS releases, implementing improved data handling so that notifications marked for deletion are no longer retained in a way that exposes their contents.
As is typical with Apple security fixes, the company has not publicly confirmed whether the vulnerability was actively exploited in the wild or provided full technical details, stating that it does not disclose specifics until patches are widely available.
Still, the context around the bug has raised concerns.
The vulnerability reportedly came to light after investigations revealed that deleted messages could be reconstructed from system-level data rather than the apps themselves, a distinction that highlights how privacy can be undermined not by app design, but by underlying operating system behaviour.
Even encrypted messaging apps weren’t immune.
Apps like Signal are designed so that messages disappear or are inaccessible once deleted, but if the operating system retains a copy in notifications, that protection can be bypassed indirectly.
That’s what makes this issue particularly significant.
It wasn’t a failure of encryption.
It was a failure of data lifecycle management at the OS level.
Privacy experts have long warned that metadata and system-level artifacts, logs, caches, notifications can sometimes reveal more than the primary data itself. This incident appears to reinforce that concern, showing how even well-secured applications can be exposed through unintended system behaviour.
Apple’s fix closes that specific gap, but it also raises a broader question about modern device security.
As smartphones become more complex, with layers of caching, syncing, and background processing, the definition of “deleted” becomes less straightforward. Data can persist in places users don’t see and don’t expect.
And in a world where devices increasingly hold sensitive conversations, financial data, and personal information, those hidden layers matter more than ever.
For users, the immediate takeaway is simple: update your device.
For the industry, the takeaway is bigger.
Privacy isn’t just about encryption or app design anymore.
It’s about ensuring that every layer of the system from apps to notifications to storage behaves exactly as users believe it does.
Because when it doesn’t, even deleted data may not be as gone as it seems.
Discover more from TechBooky
Subscribe to get the latest posts sent to your email.