The BlueHammer Windows exploit leak highlights serious issues with Microsoft’s vulnerability disclosure process and security response.
A newly leaked Windows zero-day exploit is doing more than exposing a serious vulnerability, it’s exposing cracks in how one of the world’s biggest software companies handles security itself.
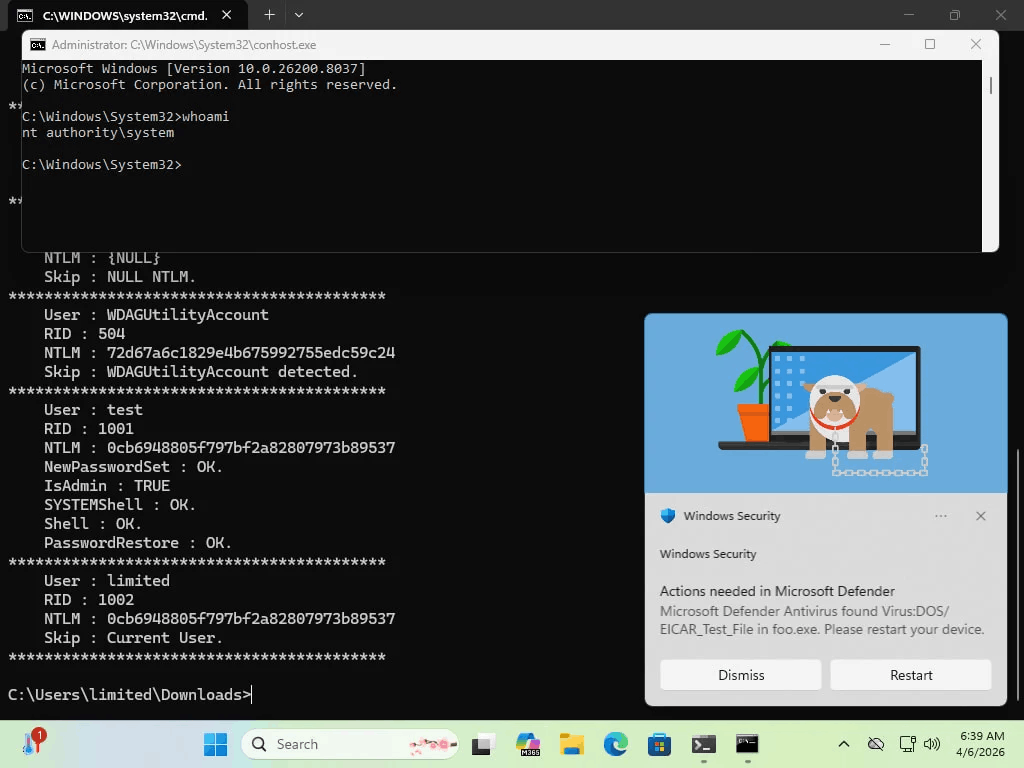
The exploit, known as BlueHammer, allows attackers with limited access to a system to escalate privileges all the way to full administrative control effectively handing over the keys to the machine.
But the real story isn’t just the vulnerability.
It’s how it got out.
The exploit was publicly released by a security researcher operating under the alias “Chaotic Eclipse,” who reportedly grew frustrated with how Microsoft handled the disclosure process. Instead of waiting for a fix, the researcher dropped working proof-of-concept code online turning a private issue into a global security risk overnight.
That move instantly transformed BlueHammer into a true zero-day, a vulnerability with publicly available exploit code but no official patch.
And that’s where things get dangerous.
Security researchers say the exploit targets core Windows mechanisms, abusing legitimate system features in a way that allows attackers to bypass protections and access sensitive components like the Security Account Manager (SAM) database where password hashes are stored.
Once inside, attackers can elevate privileges to SYSTEM level, move laterally across networks, and take full control of compromised machines.
Even more concerning is that the exploit doesn’t rely on traditional malware techniques. Instead, it chains together normal Windows processes in unexpected ways — making detection and mitigation significantly harder.
To be clear, the attack requires some level of initial access.
But in modern threat environments where phishing, credential theft, and initial breaches are common, that’s often not a meaningful barrier.
What’s raising eyebrows across the cybersecurity community is the breakdown in coordination.
The industry typically relies on responsible disclosure, where researchers privately report vulnerabilities and vendors fix them before details go public. In this case, that process appears to have failed with the researcher choosing exposure over patience.
Microsoft, for its part, has issued only a standard response emphasizing its commitment to investigating security issues and supporting coordinated disclosure practices.
But critics say that’s no longer enough.
Because once exploit code is public, the clock starts ticking.
Threat actors including ransomware groups and advanced persistent threat (APT) actors are known to rapidly weaponize publicly available proof-of-concept exploits, sometimes within days.
That puts organizations in a difficult position: defend against an active threat without an official patch.
The BlueHammer incident is now being viewed as more than just another vulnerability, it’s a signal that the relationship between security researchers and big tech companies is under strain.
And if that trust continues to break down, the next zero-day might not just be leaked.
It might be weaponized before anyone has time to respond.
Discover more from TechBooky
Subscribe to get the latest posts sent to your email.