Online security is one of the biggest issues facing our world today. From computer bugs to ransomware; fake emails and texts, or even being scammed doing an online business, everyone has to be careful to be as safe as possible online.
To start with, it is advisable to check how much of a danger one might actually be in already before embarking on the journey of being actually safe. Check out “have I been pwned?” which is an online service that analyses known data breaches. All you need to do is type in your email address to search against their findings. If you get no results, that is actually a good thing. However, if you find that your email address has actually been included in the data league, you now know where to start your password changing journey. You might be wondering “what exactly defines a secure password, and how do you make one?

Making a secure password is actually as easy as it comes. Password managers have helped to make creating and knowing your password easy. Software like Keepass and various others actually help out in this. It is not important which one you use, just that you use one of them. Keepass is an offline password manager that is free to use and extremely secure. Simply install it on your machine and run it. When it is run, you are met with a blank canvass. Start by setting up your master password which will allow you access to anything you store here, then you can begin to add the online accounts that you wish to secure a little bit further. Use the password generator that is built into most password managers to give you an amazingly secure password. Most sites keep you logged in for a certain amount of time, but when that expires, it is time to log in again. Just have your password manager to quickly remind you of how ridiculous your password is and then you can log back in.
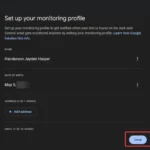
It obviously requires a little bit of legwork to get the password manager set up and running; but once you do it, you will be all set for the future and you won’t have to constantly worry about the “oh I forgot my password” syndrome that leads most of us to creating a password that can be so easy to guess and leaving us very much exposed to hacks. You can still take your security to a higher level with the two factor authentication. This might be by having to type in something more than your password to log in (such as a One Time Password O.T.P) that was sent to your phone or using an authenticator app on your phone. Most of the big sites support this feature already. Facebook is a good example of this type of sites and I can personally suggest the Google authenticator app if you need an authenticator app for your phone. Once your accounts are linked, there is no way anyone will get into your sites without your authentication code.
Another thing to think about is locking down your laptop and desktop. You can actually turn your old flash drive into an unlock key with some simple software called a USB raptor. It is safe and fairly straightforward to use. Simply install the software on your system, plug in your USB and create a code that locks your system from the software. Anytime you need to leave your system on without you being there, simply unplug the USB and your system will automatically be locked preventing anyone from snooping around. When you come back, simply plug in your USB back and the system comes back on. Just remember never to delete that single file that stores the software itself, otherwise you will be locked out of your own system.
As a last line of defense, you can always use a phone with a number that no one but you knows as a device to store your passwords or as the line for your two factor authentication. To gain access to your passwords, hackers sometimes spoof your phone number to receive your messages. Which means someone can get past your two step authentication; but not if your name or number is not even tied to the number at all, and you are the only one with access to the phone. You can keep this phone in your most secured location as a last line of security.
These are some of the ways to protect yourself from random attacks outside the normal anti-virus and firewall protection. I hope it is worth a try.
Discover more from TechBooky
Subscribe to get the latest posts sent to your email.